NIS Directive and the energy sector: a patchwork of national implementations
The energy infrastructure constitutes a foundational part of a modern society, and disturbances within its functions can have far-reaching social and economic effects across borders. During the last decade, cyber-attacks directed at the energy sector have made headlines under the names of Stuxnet, DragonFly 2.0, Flame and Black Energy. This increasing threat compounded by rapid digitalization has brought the energy sector at the forefront of the cyber security discussion.
There are three main challenges related to cybersecurity in the energy sector. The first challenge lies in the consequences, which may be severe and will also be felt immediately. In addition, problems in one network can easily cascade to other networks, thereby multiplying the effect. Finally, energy infrastructure consists both of legacy and state of-the-art technology, making the system as a whole very vulnerable.
The Directive on Security of Network and Information Systems (Directive 2016/1148, "NIS Directive") was passed in 2016 to address some of those challenges. The NIS Directive is applicable since May 2018 after it had been implemented in the Member States. In its core, the Directive aims to oblige Operators of Essential Services ("OES") to take appropriate security measures and to notify serious cyber incidents to the relevant national authority.
Even though the Directive has brought uniformity to the cybersecurity obligations of the energy sector within the EU, there still are significant national variations concerning the energy sector. In this short article we look at four areas where national laws differ in their implementation: the criteria for identification of OES in the energy sector; the method of identifying OES; notification obligations; and guidance on cybersecurity.
Criteria for identification as an OES in the energy sector
Operators of essential services in the energy sector, as identified in Annex II of the NIS Directive, generally include operators administering the provision, distribution and transmission of electricity, gas and oil. Given the minimum harmonization approach of the Directive, several EU Member States have also identified OES beyond its scope, including undertakings in thermal industry, heat supply, mining, radioactive waste management as well as supply of research, equipment and services to the energy sector. Several states, such as Germany, Spain and the UK (still an EU member at the time of NISD implementation) included power generation in the electricity subsector despite the NIS Directive not directly referring to the function “generation” in Annex II, but only included power generation in Recital 28.
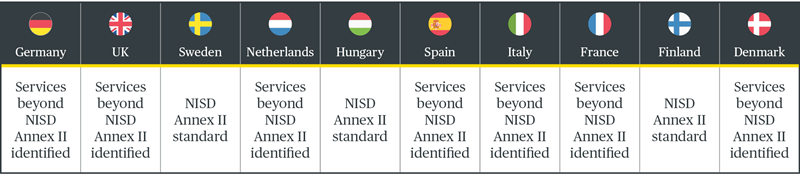
Source: Report by the NIS Cooperation Group, 9 Oct 2019 Sectorial implementation of the NIS Directive in the Energy sector
Under the Directive's regime, each Member State sets criteria for essential services; identifies operators of essential services; and maintains a list of its essential services. Some of the countries had methods and approaches in place before the release of the NIS Directive, while others developed new methodologies. The EU Commission has observed consistency gaps in identification of operators of essential services in different Member States, which could result in an uneven playing field within the internal market. Those entities who operate across the border may fall under multiple Member States’ jurisdiction if they meet the criteria of an operator of essential service in more than one country by offering their services. In addition to categories of essential services, differences in national methodologies exist, for instance, with regard to use of thresholds and assessment of network and information systems dependence.
Ongoing changes in the energy system, such as the increase in distributed and localized energy resources along with the increasing use of emerging smart energy technologies will require the national competent authorities to constantly review their approach to identification and classification of operators of essential services.
Identification of OES in practice
The process of identifying essential service operators varies between EU Member States. Some Member States put the onus on entities to determine their status under the NIS Directive. Those Member States define criteria in legislation or administrative orders and concerned companies must then notify the competent supervisory authorities. Supervisory authorities generally offer guidance to undertakings unsure of their status. As an example, the UK uses self-identification, but the supervisory authority also has the powers to independently designate an entity as operator of essential service if the authority observes it to fulfill certain criteria.
The other basket contains the Member States where relevant authorities or ministries designate the operators of essential services. The Netherlands carried their list of vital operators related to the energy sector over from the pre-existing legal act to the new Security of Network and Information Systems Decree.

Notification obligations
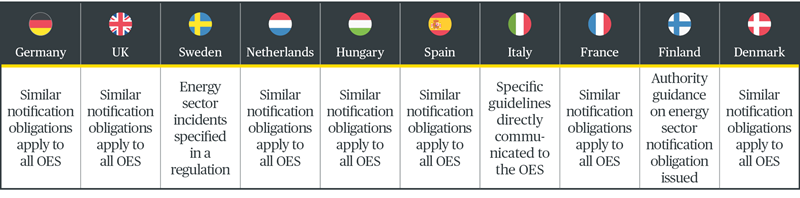
The NIS Directive requires cyber risk management and incident reporting obligations. Operators of essential services in the energy sector must notify incidents that have a significant impact on the continuity of their services. Depending on the Member State, OES must notify authorities or national contact points of incidents. Notification procedures in Member States vary and some have notification obligations specific to the energy sector. For example, Sweden has specified the nature of energy sector incidents to be notified in a decree, and in Finland the Energy Authority has issued a guidance stating that (in the first stage – likely to be followed by further guidance) the relevant operators of essential services must report every incident that has or could have affected certain of their operations.
It is common among Member States to have a uniform notification channel and process for OES’ of all sectors. Italy, for instance, has a centralized system where all operators of essential services notify their cyber security incidents to CSIRT Italia, but sectoral authorities may define the thresholds and modalities for notification in specific guidelines they directly communicate to the relevant operators.
Several countries, such as Germany, UK, Sweden, Denmark and Italy have published sector specific cyber security guidance to help energy sector companies focus their efforts. Others, such as Netherlands, Hungary, Spain, France and Finland, along with the NIS Cooperation Group and the European Union Agency for Cybersecurity have published general cybersecurity guidance and best practices. Many of the requirements brought by the NIS Directive have existed previously in national legislation in one form or another.
OES or other companies in the energy sector concerned about their obligations should therefore not only consult the relevant legislation implementing the NIS Directive, but also existing guidance.
Our energy digitalization team would be delighted to assist and to provide advice on defining OES status, registration and all other aspects of NIS Directive.
Further resources:
Developments on NIS Directive in EU Member States >
Bird & Bird NISD Tracker >
More articles by the Bird & Bird cybersecurity team >