Big Data & Issues & Opportunities: Cybersecurity
In this fourth article in our series on "Big Data & Issues & Opportunities" (see our previous article here), we focus on some of the cybersecurity aspects of big data processing. Where relevant, illustrations from the transport sector will be provided.
Given that cyber-threats and attacks may have devastating consequences, the issues related to cyber-security have never been more important. For instance, in the transport sector, cyber-attacks could have potentially serious consequences on the economy but also on individuals, resulting in certain cases in loss of lives.[1]
It follows that any organisation, including notably actors in the big data value chain, is required to observe the legal obligations related to security and cyber-security, which derive not only from the General Data Protection Regulation (hereinafter the "GDPR")[2], but also from other legislative instruments at both EU and national level.
The present article will look into such security requirements under the GDPR, the Network and Information Security Directive (hereinafter the "NIS Directive")[3], and other European legislations and security standards.
Security requirements under the GDPR
The requirements relating to security under the GDPR apply whenever personal data is processed (see our second article on Privacy & Data Protection for the definitions of "processing" and "personal data"). Considering that the use of big data technologies may entail massive personal data processing operations, the GDPR security requirements will have to be taken into account in such context.
The GDPR security requirements can be divided into, on the one hand, personal data governance obligations and, on the other hand, obligations relating to the security of personal data processing.
As regards the personal data governance obligations laid down in the GDPR, a general obligation is imposed upon data controllers to adopt technical and organisational measures to ensure compliance with the GDPR and, importantly, to be able to demonstrate such compliance.[4] Operating a regular audit programme, implementing privacy by design and by default measures, running data protection impact assessments, appointing a data protection officer, etc. are all measures considered to be in line with the data governance obligations, including the security-related requirements. Such measures must be reviewed and updated on a regular basis, taking into account the changing circumstances.
As for the obligations relating to the security of personal data processing, the GDPR requires data controllers and processors to implement appropriate technical and organisational measures to ensure a level of security appropriate to the risk.[5] In the context of big data, this entails that both data controllers and processors should continuously evaluate, manage, and document the risks involved in their respective processing activities.[6] The GDPR does not detail the security measures that can or should be put in place. It nonetheless provides some, however limited, specific suggestions for what types of security measures might be considered “appropriate to the risk”.[7]
The GDPR moreover indicates that adherence to an approved code of conduct or certification mechanism may be used as an element to demonstrate compliance with data governance obligations[8] as well as with security requirements.[9] Currently, such codes of conduct or certification mechanisms are still being developed throughout the EU market.
Finally, it should be borne in mind that the GDPR imposes a high duty of care upon data controllers in the selection of personal data processing service providers, i.e. their processors.[10] In a data-rich environment, such as in the context of big data processing operations, the data controller should carefully impose security obligations in its respective agreements concluded with processors, including for instance cloud service providers. Also, it shall be contractually ensured that a processor relying on a sub-processor imposes security obligations on such sub-processor equivalent to those imposed by the controller on the processor.
Security requirements under the NIS Directive
The NIS Directive was adopted on 6 July 2016 to address the increasing challenges in relation to cybersecurity.[11] This EU legislation aims to develop a common approach across Europe to address potential socio-economic damage caused by attacks on the network and information systems of operators of essential services and digital service providers.
Taking into account its nature as a directive, the NIS Directive had to be implemented by the EU Member States into their national laws by May 2018.[12] It is therefore required to carefully consider the specific obligations flowing from the national implementing laws, which may be particularly relevant in a big data context, but also in the transport sector.
The Directive imposes (online) security obligations on providers of two different types of services discussed hereunder: essential and digital services.
- Essential service: Article 5 of the NIS Directive defines an essential service as "a service essential for the maintenance of critical societal and/or economic activities depending on network & information systems, an incident to which would have significant disruptive effects on the service provision."
EU Member States had to identify the operators of essential services established on their territory by 9 November 2018. Operators active in the following sectors may be included: energy, transport, banking, stock exchange, healthcare, utilities, and digital infrastructure.[13]
|
Illustration in the transport sector: The transport sector may provide services the NIS Directive considers to be essential. All modes of transportation are concerned[14], provided both by public and private entities[15]. The NIS Directive classifies in an Annex the following transportation modes:
|
- Digital service: a digital service is defined as "any service normally provided for remuneration, at a distance, by electronic means and at the individual request of a recipient of services" and which can be qualified as one of the following: (i) an online marketplace; (ii) an online search engine; or (iii) a cloud computing service.[16]
In contrast with the operators of essential services, which are identified by each EU Member State, online businesses must self-assess whether they are targeted by the rules of the NIS Directive, and in particular whether they fall within one of the three different types of digital services mentioned above.
The fact that cloud computing services are targeted by the NIS Directive is particularly relevant in a big data context, especially in light of its broad definition; i.e. a digital service that enables access to a scalable and elastic pool of shareable computing resources. This being said, other stakeholders in the (big) data value chain, taking an active role in the provision of services (such as in the transport sector), may also be concerned by different concepts of the NIS Directive. It seems likely that the big data value chain will include operators of online market places (generally described as operators of platforms that act as an intermediary between buyers and sellers), online sites that redirect users to other services to conclude contracts or facilitate trade between parties, and sites that sell directly to consumers.
Finally, it shall be noted that even if a particular actor of the data value chain would not be qualified as a digital service provider or an operator of essential services, the NIS Directive obligations may indirectly apply to suppliers of digital or essential service providers as a result of flow down obligations.
|
Illustration in the transport sector: The application of the NIS Directive may lead to complex situations. An integrated urban mobility plan can illustrate the possible complexity, where for instance, the plan aims to meet the following three key objectives[17]:
In order to fulfil the above objectives, many actors may come into play that could qualify as operators of essential services and digital service providers or that could be obliged to take into account the NIS Directive due to flow down obligations. Indeed, in such context, road authorities responsible for traffic management control and/or operators of Intelligent Transport Systems are likely to be involved. Similarly, cloud computing service providers will be relied on. Finally, ‘online market places’ could be involved and targeted by the NIS Directive rules in the context of the third objective.[18] |
Under the new rules of the NIS Directive and the national implementing legislations, the essential and digital service providers will have to (i) interact with new key actors; (ii) implement security measures; and (iii) notify security incidents.
With regard to the security measures, the NIS Directive includes generic obligations by requiring operators of essential services and digital service providers to take appropriate and proportionate technical and organisational measures to manage the risks posed to the networks and information systems which they use for the provision of their services, and to prevent and minimise the impact of incidents affecting the security of such network and information systems.[19] These security measures must take into account the state of the art to ensure a level of security of network and information systems adequate to the risk.
More particularly, when examining the security aspects of Operators of Essential Services (OES) and Digital Service Providers (DSPs), it is worth considering the following:
| Security of Operators of Essential Services |
Security of Digital Service Providers |
|
|
Security requirements under other legislations
- It is important to note that other legal instruments may impose security requirements as well. This is particularly true in the electronic communications sector where several EU Directives, transposed in the national laws of the (currently) 28 Member States, provide for security obligations – such as for instance:
- The ePrivacy Directive[29]: this Directive requires providers of electronic communications services to take appropriate technical and organisational measures to safeguard the security of their services, where necessary in conjunction with the provider of the public communications network.
- The Framework Directive[30]: this complements the ePrivacy Directive by requiring providers of publicly available electronic communication networks and services to take appropriate measures to manage the risks posed to the security of the networks and services. The Directive also requires the providers to guarantee the integrity of their networks and continuity of supply.
The Radio Equipment Directive[31]: pursuant to this Directive, radio equipment within certain categories or classes shall incorporate safeguards to ensure that the personal data and privacy of users and subscribers are protected.
Security standards
In addition to legal requirements on security, security standards indisputably have an important role to play in big data analytics, and are therefore also relevant to actors of the data value chain. Also, relying on standards and certification schemes facilitates demonstrating compliance with legal requirements, including security requirements.By relying on existing schemes, such as for instance the ISO/IEC 27000 series issued by the International Standards Organisation ("ISO") and the International Electrotechnical Commission ("IEC"), big data services providers can demonstrate to the regulator and to their customers that their systems are adequate, or at least that security-related measures and processes have been implemented.
Furthermore, several standards development organisations have created and are currently developing big data-specific standards. It is essential for any big data service provider to follow up closely on the evolutions in this respect.
Security in practice: a complex reality
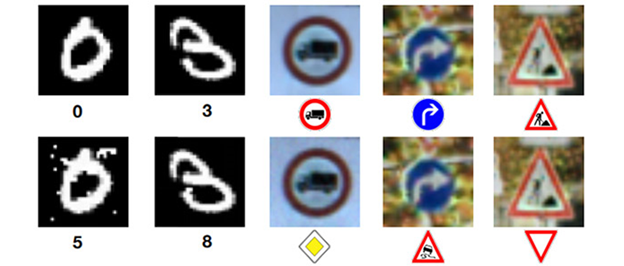
Despite the existence of guidance on the various security obligations and how to consider them practically, the implementation of security aspects remains difficult in reality and requires further and continuous research.A good way to illustrate the complexities of applying appropriate security measures is through so-called “adversarial images”. The concept of adversarial images consists in making minor changes to manipulate machine learning algorithms. To illustrate such specific security issue, OpenAI relies on the work performed by Cornell University[32]. More concretely, "starting with an image of a panda, the attacker adds a small perturbation that has been calculated to make the image be recognized as a gibbon with high confidence".[33]
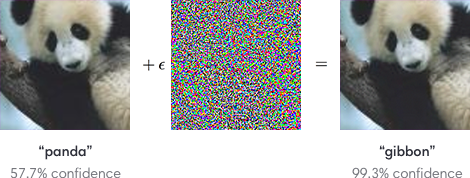
|
Illustration in the transport sector: The concept of adversarial images can be particularly relevant in the transport sector. For instance, making changes to a street sign can make the algorithm think that the signs say something completely different than they actually do. The Institute of Electrical and Electronics Engineers published an article to illustrate how “Slight Street Sign Modifications Can Completely Fool Machine Learning Algorithms”[34]. Adversarial images can cause “signs that look like one thing to us to look like something completely different to the vision system of an autonomous car, which could be very dangerous for obvious reasons.”[35] For instance, in the image below, “the top row shows legitimate sample images, while the bottom row shows adversarial sample images, along with the output of a deep neural network classifier below each image.”[36]
|
Conclusion
The requirement to put in place security measures is imposed in various legislations at EU and national level, including key instruments like the GDPR and the NIS Directive. Such legislations however remain rather general and vague as to which specific measures are deemed appropriate. It follows that organisations in the data value chain are required to:
- make a risk assessment (evaluate, manage and document the risks);
- carefully assess the available security measures on the market;
- adequately reflect the security aspects in the various contracts between stakeholders; and
- continuously assess the adequacy of the implemented measures in light of the evolving risks and the available measures.
In order to do so, organisations generally need to rely on security experts and take into account the evolving guidance documents published by authorities such as ENISA. Also, relying on certification mechanisms, seals, marks and codes of conduct will enable companies to comply with their legal obligations in terms of security and demonstrate their compliance.
Despite the enormity of the task still to be undertaken in order to improve cyber-security across the EU, the various stakeholders are aware of the need to move forward, notably through non-regulatory actions and improved cooperation. The EU institutions have also recently devised the appropriate means to tackle the cyber-security challenges, notably through the political agreement on 11 December 2018 by the European Parliament, the Council and the European Commission on the so-called "Cybersecurity Act" which aims to reinforce the mandate of ENISA and establish an EU framework for cybersecurity certification.[37]
Our next article will address breach-related obligations in the context of big data, with illustrations drawn from the transport sector.
 This series of articles has been made possible by the LeMO Project (www.lemo-h2020.eu), of which Bird & Bird LLP is a partner. The LeMO project has received funding from the European Union’s Horizon 2020 research and innovation programme under grant agreement no. 770038.
This series of articles has been made possible by the LeMO Project (www.lemo-h2020.eu), of which Bird & Bird LLP is a partner. The LeMO project has received funding from the European Union’s Horizon 2020 research and innovation programme under grant agreement no. 770038.
This article on (cyber-)security has also been made possible by the THREAT-ARREST Project (www.threat-arrest.eu), of which Bird & Bird LLP is a partner. The THREAT-ARREST Project has received funding from the European Union’s Horizon 2020 research and innovation programme under grant agreement no. 786890.
The information given in this document concerning technical, legal or professional subject matter is for guidance only and does not constitute legal or professional advice.
The content of this article reflects only the authors’ views. The European Commission and Innovation and Networks Executive Agency (INEA) are not responsible for any use that may be made of the information it contains.
[1] Joint statement of the European Commission, ENISA, EMSA, EASA and ERA of 23 January 2019, "Transport cybersecurity: Raising the bar by working together" in the context of the 1st Transport Cybersecurity Conference held in Lisbon.
[2] Regulation (EU) 2016/679 of the European Parliament and of the Council of 27 April 2016 on the protection of natural persons with regard to the processing of personal data and on the free movement of such data, and repealing Directive 95/46/EC (General Data Protection Regulation) [2016] OJ L 119/1
[3] Directive (EU) 2016/1148 of the European Parliament and of the Council of 6 July 2016 concerning measures for a high common level of security of network and information systems across the Union [2016] OJ L 194/1
[4] GDPR, art 24
[5] Such measures shall take into account the following elements: (i) the state of the art; (ii) the costs of implementation; (iii) the nature, scope, context, and purposes of the processing; and (iv) the risk of varying likelihood and severity for the rights and freedoms of natural persons.
[6] Commission de la protection de la vie privée, 'Big Data Rapport' (CPVP 2017) 58 <https://www.autoriteprotectiondonnees.be/sites/privacycommission/files/documents/Rapport_Big_Data_2017.pdf> accessed 10 January 2019.
[7] Pursuant to Article 32(1) GDPR, these are (i) the pseudonymisation and encryption of personal data; (ii) the ability to ensure the on-going confidentiality, integrity, availability and resilience of processing systems and services; (iii) the ability to restore the availability and access to personal data in a timely manner in the event of a physical or technical incident; and (iv) a process for regularly testing, assessing and evaluating the effectiveness of technical and organisational measures for ensuring the security of the processing.
[8] GDPR, arts 24(3) and 28(5)
[9] GDPR, art 32(3)
[10] GDPR, art 28(1)
[11] Cybercrime is indeed predicted to cost the world over $ 6 trillion per year by 2021, see Mark Hue Williams and Jamie Monck-Mason, 'Guide to the NIS Directive for Transportation Companies' (Willis Towers Watson, 8 August 2017) <https://www.willistowerswatson.com/en/insights/2017/08/guide-to-the-nis-directive-for-transportation-companies> accessed 10 January 2019.
[12] NIS Directive, art 25. EU Member States had 21 months to transpose the Directive into their national laws and 6 additional months to identify the providers of essential services subject to the Directive's requirements.
[13] NIS Directive, Annex II
[14] NIS Directive, Annex II
[15] NIS Directive, art 4(4)
[16] NIS Directive, art 4(5)
[17] Transforming Transport, 'Integrated Urban Mobility: Tampere Pilot' (TT, 2018) <https://transformingtransport.eu/transport-domains/integrated-urban-mobility-tampere-pilot> accessed 10 January 2019
[18] Online market places’ are defined broadly as any digital service that allows consumers and/or traders to conclude online sales or service contracts with traders either on the online marketplace's website or on a trader's website that uses computing services provided by the online market place
[19] NIS Directive, arts 14 and 16
[20] European Union Agency for Network and Information Security, 'Mapping of OES Security Requirements to Specific Sectors' (ENISA 2018) <https://www.enisa.europa.eu/publications/mapping-of-oes-security-requirements-to-specific-sectors> accessed 10 January 2019
[21] NIS Cooperation Group, 'Reference Document on Security Measures for Operators of Essential Services' (European Commission 2018) <
[22] Ibid 5
[23] No further security requirements shall be imposed on digital service providers, aside from requirements for the protection of essential State functions and for the preservation of law and order (NIS Directive, art 16(10) juncto art 1(6)).
[24] NIS Directive, art 16(1)
[25] European Union Agency for Network and Information Security, 'Technical Guidelines for the Implementation of Minimum Security Measures for Digital Service Providers' (ENISA 2016) <
[26] Commission Implementing Regulation (EU) 2018/151 laying down rules for application of Directive (EU) 2016/1148 of the European Parliament and of the Council as regards further specification of the elements to be taken into account by digital service providers for managing the risks posed to the security of network and information systems and of the parameters for determining whether an incident has a substantial impact [2018] OJ L 26/48
[27] Joint statement of the European Commission, ENISA, EMSA, EASA and ERA of 23 January 2019, "Transport cybersecurity: Raising the bar by working together" in the context of the 1st Transport Cybersecurity Conference held in Lisbon.
[28] Ibid.
[29] Directive 2002/58/EC of the European Parliament and of the Council concerning the processing of personal data and the protection of privacy in the electronic communications sector [2005] OJ L 201/37 (ePrivacy Directive). Please note that the e-Privacy legislation is currently being reviewed and that the European Commission has issued a Proposal for an ePrivacy Regulation.
[30] Directive 2002/21/EC of the European Parliament and of the Council on a common regulatory framework for electronic communications networks and services [2002] OJ L 108/33 (Framework Directive). Please note that this Directive will be repealed as from 21 December 2020, in accordance with the newly adopted Directive (EU) 2018/1972 of the European Parliament and of the Council of 11 December 2018 establishing the European Electronic Communications Code.
[31] Directive 2014/53/EU of the European Parliament and of the Council of 16 April 2014 on the harmonisation of the laws of the Member States relating to the making available on the market of radio equipment and repealing Directive 1999/5/EC [2014] OJ L 153/62 (Radio Equipment Directive).
[32] Ian J. Goodfellow, Jonathon Shlens and Christian Szegedy, 'Explaining and Harnessing Adversarial Examples' (2015) <https://arxiv.org/abs/1412.6572> accessed 10 January 2019
[33] Ian Goodfellow and others, 'Attacking Machine Learning with Adversarial Examples' (OpenAI, 24 February 2017) <
[34] Evan Ackerman, 'Slight Street Sign Modifications Can Completely Fool Machine Learning Algorithms' (IEEE Spectrum, 4 August 2017) <https://spectrum.ieee.org/cars-that-think/transportation/sensors/slight-street-sign-modifications-can-fool-machine-learning-algorithms> accessed 10 January 2019
[35] Ibid
[36] Ibid
[37] European Commission press release of 11 December 2018 available at <https://ec.europa.eu/commission/news/cybersecurity-act-2018-dec-11_en>, accessed 25 January 2019 .